Quantum mechanics creates location-based cryptography
Source: io9.com
Imagine a form of encrypted communication so secure that it’s physically impossible to access it unless you’re actually at the location where you’re supposed to hear it. Quantum mechanics makes location-based cryptography possible - without any pesky codes or keys.
The basic idea is simple - create an encrypted communication where your actual physical location is the only key required to gain access to the hidden information. It would eliminate any need to create and store decryption keys, which is disproportionately the most complex and time-intensive task in cryptography. You could encrypt a secure line so that the only people who could ever hear would have to be at, say, two secure military bases, eliminating any chance of someone listening in from a third location.
And now computer scientists at UCLA have figured out how to do it. The big problem holding back location-based cryptography was that triangulation, the classical method of verifying the receiver’s location is the correct one, can be forged if enemies work together to provide just the right combination of wrong information. But that’s just classical physics - quantum mechanics has that problem solved. The solution lies in the no-cloning theorem, an outgrowth of the uncertainty principle that basically states it’s impossible to create an exact replica of a quantum state.
This means that, when the secure transmitter sends out multiple quantum bits, or qubits, the intended receiver is the only device that can verify the information and confirm they are who they say they are. If an adversary was trying to listen in, they’d still need multiple transmitters to mimic the supposed location, but that’s now physically impossible because the first adversary would need to both store the qubit’s state and send it on to the next confederate, and quantum mechanics says that’s impossible.
As the authors note in their abstract:
Therefore, our work shows that position-based quantum cryptography is one of the rare examples...for which there is such a strong separation between classical and quantum cryptography. Our results open a fascinating new direction for position-based security in cryptography where security of protocols is solely based on the laws of physics and proofs of security do not require any pre-existing infrastructure.
Article from: io9.com
Also tune into:
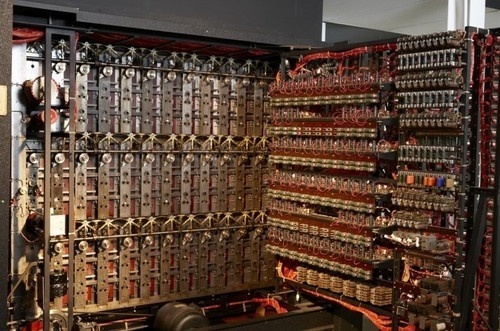
Nick Pelling - The Voynich Manuscript, Alan Turing and Ciphers
Nick Pelling - Deciphering of the Mysterious Voynich Manuscript
Jim Gardner - The Intelligent Universe, Bio-Cosm, ET, AI and Evolution